MS Notepad RCE Exploit (CVE-2026-20841)
Overview of the Vulnerability
Microsoft Notepad in versions prior to 11.2510 is affected by a vulnerability leveraged by using a flaw in validation of Markdown file links. Attackers could exploit this vulnerability by crafting a malicious Markdown (.md extension) file, that once opened by a victim would execute an untrusted URI. This execution could launch or retrieve local or remote files without standard Windows security validation.
Markdown is a lightweight markup language that allows users to format text into a structured document using a defined syntax. It is used in code documentation, blogging, messaging and note taking applications for simple, readable formatting.
Markdown Links and Their Role in the Exploit
The feature of Markdown core to this exploit is link formatting. Syntax to embed a link into a document is [link-name](URI). For example, to link Google, this feature can be leveraged by using [Google](https://www.google.com/) which in a rendered document will be shown as Google.
How the Vulnerability Works
So how is this used in this RCE? When user opens an .md file with Notepad the application understands that the file needs special rendering. To render the Markdown code, input is initially tokenized – raw text is split into pieces that the renderer can process. Then calls are made to a series of functions that handle the rendering itself. The culprit behind this exploit is a function that handles links in Markdown files.
This function has been decompiled to find the way it parses and sanitizes links. You can find original code linked at the end of the article.
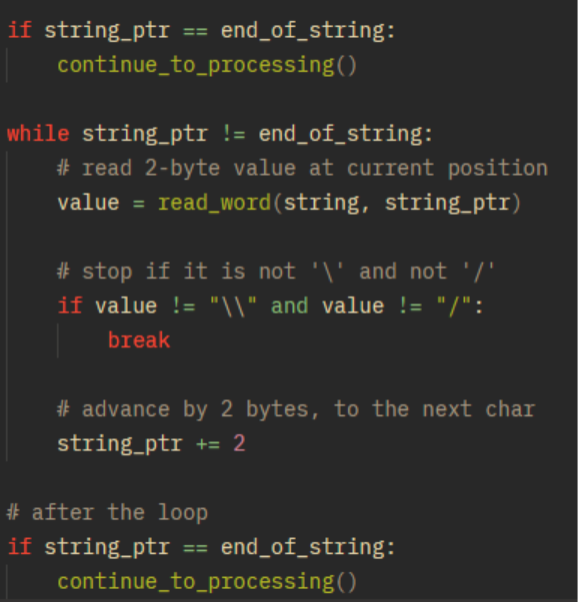
Sanitization is rudimentary. It is handled by a single loop that checks whether there is just one character that isn’t a ‘\\’ or ‘/’. The moment it finds any other character the loop breaks and code proceeds. (This is python-like pseudocode, derived from original code: line 52 onwards).
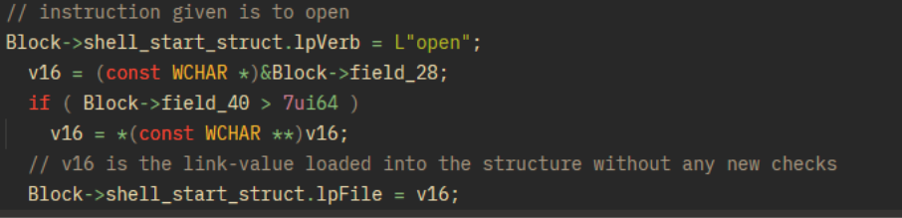
After this, only backslashes from the end are trimmed and the value is loaded into a SHELLEXECUTEINFOW structure that configures the process to be launched. Important lines of code are from line 112 onwards. We can see that the instruction is to open and that the link value is loaded without any further sanitization.
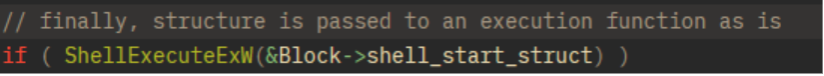
This structure is then passed to a ShellExecuteExW() Windows API function (line 133 in original code) that launches or interacts with files, executables and URIs.
Root Cause and Impact
The core issue behind this exploit is the lack of any kind of link sanitization, check or filtering. The structure that starts a process is loaded with raw URI provided by the attacker. No Windows Security features are implemented to stop this, essentially any kind of behavior is allowed.
This exploit has been fixed in Notepad patch 11.2510.
Sources:
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2026-20841
https://threatlandscape.io/blog/vulnerability-spotlight-cve-2026-20841?utm_source=chatgpt.com
Decompiled code:
Prepared by Verso Altima
Security Research Team

